One of the key features to look for in a firewall is its ability to block zero-day malware. This type of threat has become such a focus because modern anti-virus and anti-malware solutions are typically unable to stop them. The primary feature of a zero-day threat is that it’s unknown, meaning anti-virus and anti-malware solutions don’t yet have a signature for it and therefore can’t stop it. Threats such as ransomware fall into this category, which is why they can cause such havoc for an organization.
Due to the rising amounts of these threats that a network must deal with, threat protection is a must for every organization. That’s why it’s important to understand the two categories available:
Threat Protection (noun): A service that is designed to identify threats on a network.
Threat Protection (verb): The act of blocking threats on a network.
With the WatchGuard firewall, one of the services available to stop threats is APT (Advanced Persistent Threat) Blocker. The APT Blocker service is designed to use a sandbox environment to help look for these threats so that we are not relying solely on a signature. The biggest thing to be aware of with APT Blocker is that it is using the “noun” approach.
Licensing
APT Blocker is included as part of the Total Security Suite, or as a standalone service. APT Blocker is available for all currently supported XTM, T-series and M-series devices.
Antivirus Dependency
There are several key pieces to understand about APT Blocker. The first is that, in order for it to work, Gateway Antivirus must first be configured on the firewall. This is because APT Blocker piggybacks off of the same scanning engine. So, if you don’t have GAV turned on for your Web (HTTP/HTTPS), FTP and email proxies, APT Blocker won’t be able to scan the content.
NOTE: When dealing with web traffic, GAV and APT Blocker will only work on HTTPS if you have Deep Packet Inspection configured.
File Processing
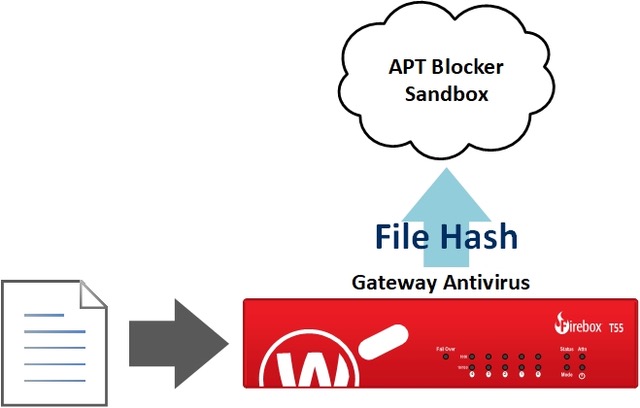
The other important piece to understand about APT Blocker is how files are actually processed.
When the firewall is processing a file, it is first scanned by Gateway Antivirus, as long as the service is configured on the proxy.
If the file passes Gateway Antivirus’ scan, GAV will send a hash of the file to the APT Blocker cloud sandbox.
If the file hash has been seen and is known to be malicious, it can be stopped during this process, meaning the user that initiated the access never comes in contact with the threat.
If the file hash has not been seen, APT Blocker requests a copy of the file be sent to the APT Blocker Sandbox.
Active Monitoring
This last step is the most critical part in the process, and is what makes APT Blocker take the “noun” approach to threat protection instead of being a more active part of the process. Due to the nature of the sandbox environment, it could take several minutes for the scan of the file copy to finish before APT Blocker knows if it is malicious or not. So that productivity is not slowed down, the original file is sent on to the user. This means that APT Blocker is leaving a gap in security, and you must rely on your alerts being configured correctly on the firewall to understand if the service found anything.
Comprehensive Protection
JSCM Group’s stance on security is that one service or product is never enough. While APT Blocker can provide a level of protection from the firewall’s perspective, this only occurs if the file hash is known. APT Blocker’s behavior of allowing an unknown file to pass through to the user before all scanning is complete does leave a significant hole. This is why JSCM Group recommends that every device on the network be configured with local endpoint protection with threat detection capabilities. If you are interested in learning more about our recommendations for endpoint protection, please check out our page on Sophos Endpoint Protection.
For details on ensuring APT Blocker is configured correctly, please check out our APT Blocker blog post.